 |
Info-Tech's Security Priorities 2024 report delves into the pressing issues that APAC IT and security leaders must prioritise over the coming year, including the cybersecurity talent shortage, the rise of AI-driven threats, the integration of security risks with business risks, the adoption of zero-trust frameworks, and the increasing significance of automating security operations. The global IT research and advisory firm explains in the report that by addressing these priorities, organisations can better prepare themselves to face the evolving threat landscape.
SYDNEY, June 6, 2024 /PRNewswire/ -- With cyber threats becoming increasingly sophisticated, organisations are facing unprecedented challenges in safeguarding their digital assets. Recognising the urgent need for robust and dynamic security strategies, Info-Tech Research Group has published its Security Priorities 2024 report. The report underscores the critical need for organisations to adapt their security measures in response to the constant changes in cyber threats in 2024 and beyond. The firm's research highlights the importance of a strategic approach, emphasising the need for clear oversight and effective implementation strategies to develop, deploy, and monitor security initiatives that enhance an organisation's resilience against threats.
'The uptake of AI technologies across public and private sectors has added another dimension to an already challenging threat landscape,' says Robert Dang, principal advisory director at Info-Tech Research Group, APAC. 'CISOs and security leaders could expect to find themselves in a situation where they must enable the adoption of new AI technologies while managing the risks that come with its rapid evolution. On the opposite end of this situation, delays or failure to enable AI adoption could see them fall behind peer organisations and exacerbate existing challenges like developing their cyber security workforce and operationalising zero trust security.'
The Security Priorities 2024 report reveals the pressing issues that IT and security leaders must prioritise and advocate for a pivot from traditional, reactive security postures to proactive, predictive security strategies. The annual report emphasises the importance of fostering a security-centric culture across the organisation, enhancing collaboration between security teams and other business units, and developing agile security frameworks that can adapt to new threats and business needs.
'The emergence of advanced technologies has created opportunities for organisations asnd security leaders to explore unique approaches to these challenges while also enhancing existing capabilities to better equip themselves with the right people, process, and technology this year,' says Ahmad Jowhar, research analyst and lead author of the report. 'These approaches include assessing the ability to address the talent shortage through upskilling, establishing a foundation to implement AI technologies, and evaluating an organisation's security risk management with respect to integrating with the enterprise.'
Info-Tech's latest report is based on comprehensive research, including insights from the firm's Future of IT survey and in-depth interviews with IT and security professionals across various industries and regions. The diverse approach ensured that the experiences of leaders from both small and large organisations were incorporated into the report and covered a broad spectrum of security budgets. The insights collected and analysed by the firm reflect the realities of managing cybersecurity in different organisational contexts, from multinational corporations to nimble startups, providing a well-rounded view of the challenges and strategies at play in the current security landscape.
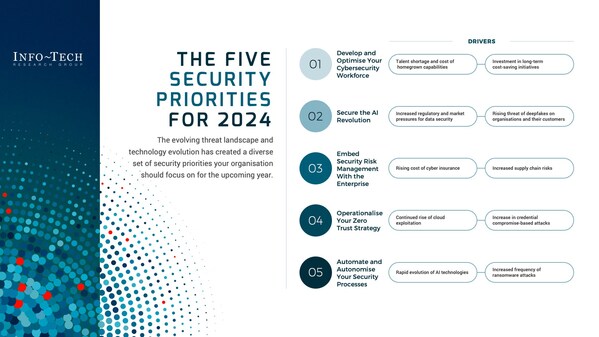
Leveraging the firm's research findings and data, the Security Priorities 2024 report outlines the following five high-priority initiatives security leaders and their organisations should implement to confidently address security risks for 2024 and the years to come:
The 2024 report also includes customisable templates that security leaders can utilise to effectively communicate their organisation's key security priorities to stakeholders and executives, ensuring a clear understanding of the required security measures.
In the face of ever-evolving cyber threats, the Security Priorities 2024 report provides security leaders with a blueprint for safeguarding their digital environment. By implementing the priorities based on their unique organisational goals and needs, security leaders can enhance their security posture, proactively address and mitigate vulnerabilities, and build a culture of resilience against the cyber threats of the future.
For exclusive media commentary from Robert Dang or Ahmad Jowhar, experts in cybersecurity and privacy, or to access the complete Security Priorities 2024 report, please contact pr@infotech.com.
Registration is now open for Info-Tech Research Group's annual IT conference, Info-Tech LIVE 2024, taking place September 17 to 19, 2024, at the iconic Bellagio in Las Vegas. This premier event will also offer journalists, podcasters, and media influencers access to exclusive content, the latest IT research and trends, and the opportunity to interview industry experts, analysts, and speakers. To apply for media passes to attend LIVE 2024 or to gain access to content and expert insights from the event, please contact pr@infotech.com.
Info-Tech Research Group is one of the world's leading research and advisory firms, proudly serving over 30,000 IT and HR professionals. The company produces unbiased, highly relevant research and provides advisory services to help leaders make strategic, timely, and well-informed decisions. For nearly 30 years, Info-Tech has partnered closely with teams to provide them with everything they need, from actionable tools to analyst guidance, ensuring they deliver measurable results for their organisations.
To learn more about Info-Tech's divisions, visit McLean & Company for HR research and advisory services and SoftwareReviews for software buying insights.
Media professionals can register for unrestricted access to research across IT, HR, and software and hundreds of industry analysts through the firm's Media Insiders program. To gain access, contact pr@infotech.com.
For information about Info-Tech Research Group or to access the latest research, visit infotech.com and connect via LinkedIn and X.